CAS-003 문제 46
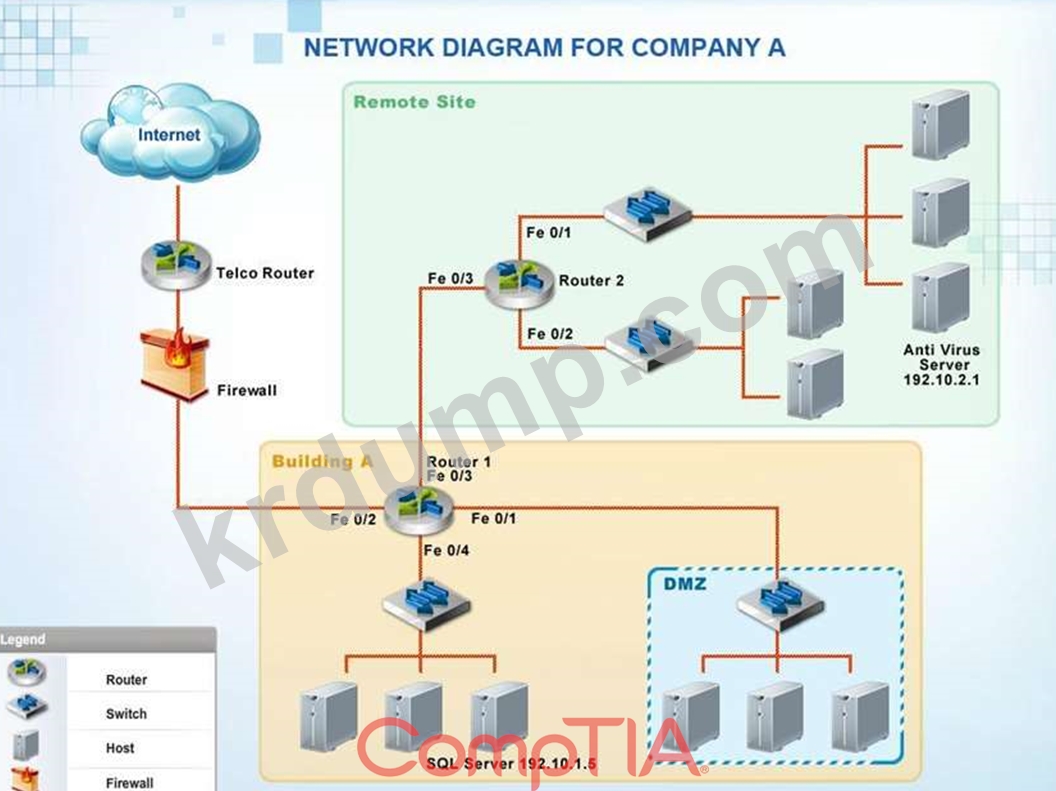
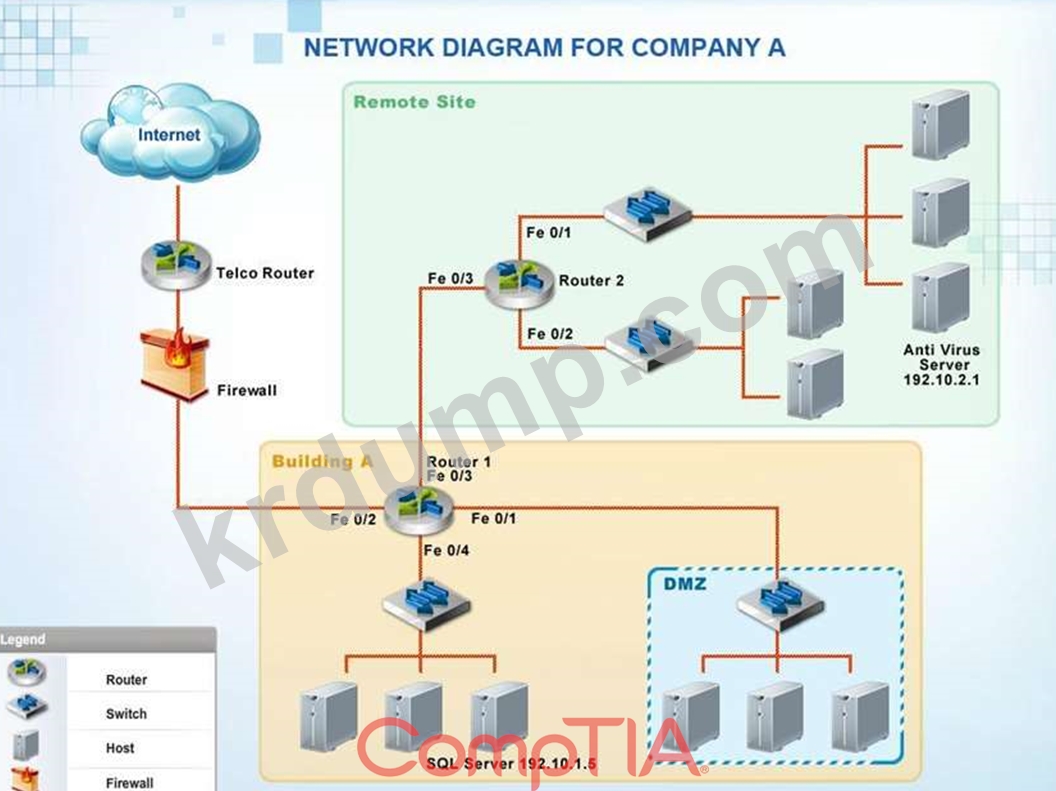
Company A has noticed abnormal behavior targeting their SQL server on the network from a rogue IP address.
The company uses the following internal IP address ranges: 192.10.1.0/24 for the corporate site and
192.10.2.0/24 for the remote site. The Telco router interface uses the 192.10.5.0/30 IP range.
Instructions: Click on the simulation button to refer to the Network Diagram for Company A.
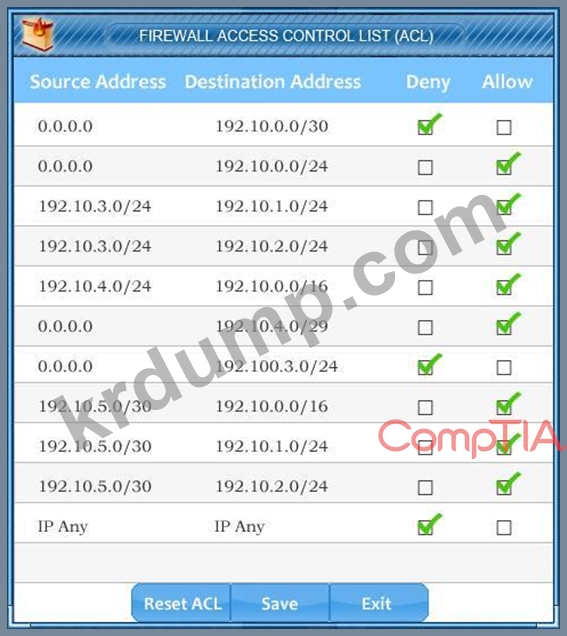
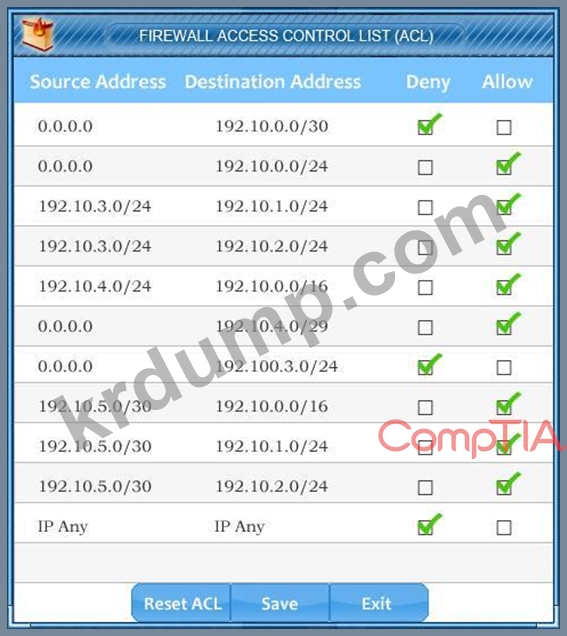
Click on Router 1, Router 2, and the Firewall to evaluate and configure each device.
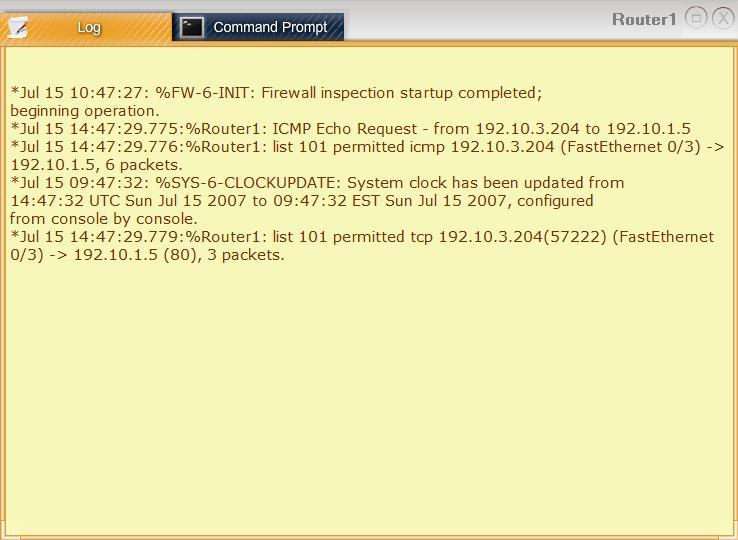
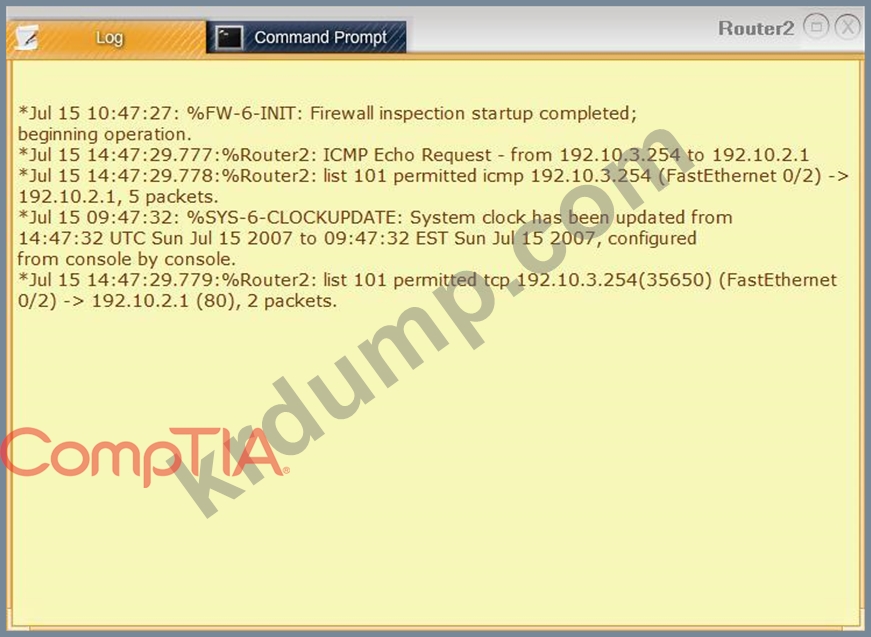
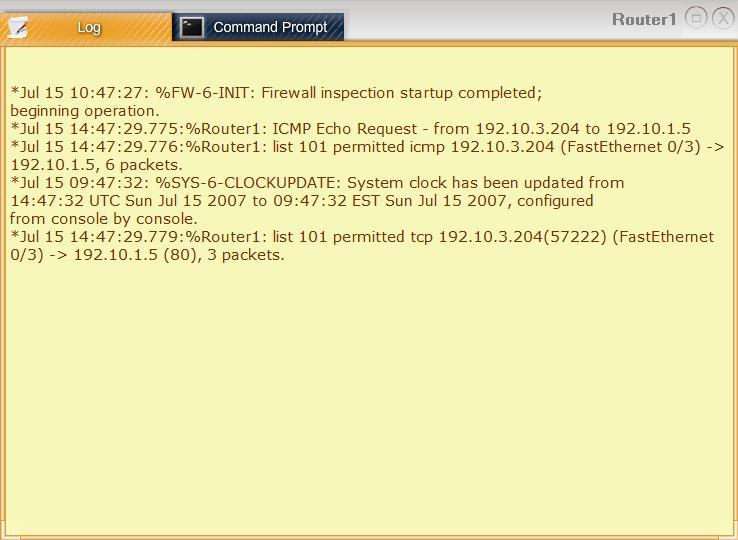
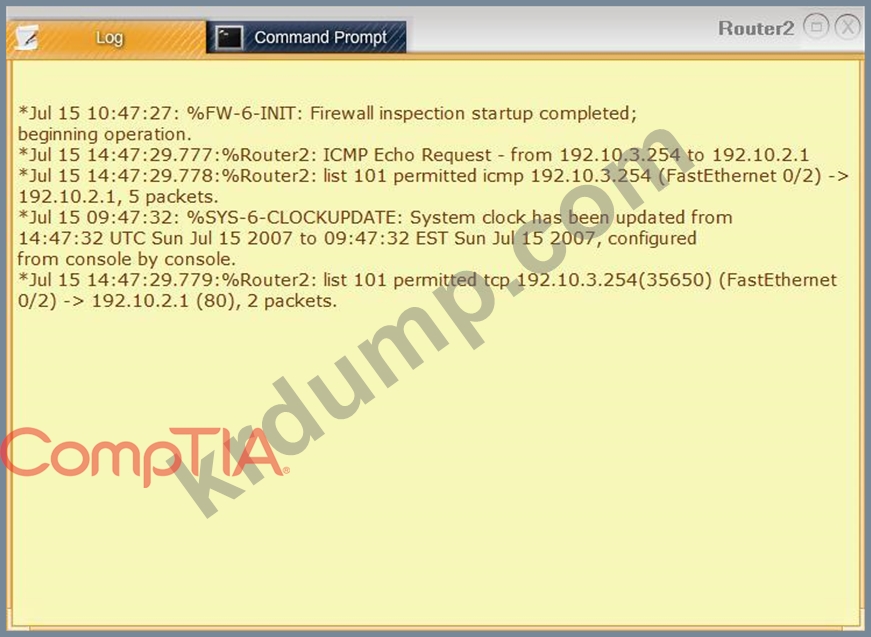
Task 1: Display and examine the logs and status of Router 1, Router 2, and Firewall interfaces.
Task 2: Reconfigure the appropriate devices to prevent the attacks from continuing to target the SQL server and other servers on the corporate network.
The company uses the following internal IP address ranges: 192.10.1.0/24 for the corporate site and
192.10.2.0/24 for the remote site. The Telco router interface uses the 192.10.5.0/30 IP range.
Instructions: Click on the simulation button to refer to the Network Diagram for Company A.
Click on Router 1, Router 2, and the Firewall to evaluate and configure each device.
Task 1: Display and examine the logs and status of Router 1, Router 2, and Firewall interfaces.
Task 2: Reconfigure the appropriate devices to prevent the attacks from continuing to target the SQL server and other servers on the corporate network.
CAS-003 문제 47
A security manager is looking into the following vendor proposal for a cloud-based SIEM solution. The intention is that the cost of the SIEM solution will be justified by having reduced the number of incidents and therefore saving on the amount spent investigating incidents.
Proposal:
External cloud-based software as a service subscription costing $5,000 per month.
Expected to reduce the number of current incidents per annum by 50%.
The company currently has ten security incidents per annum at an average cost of $10,000 per incident. Which of the following is the ROI for this proposal after three years?
Proposal:
External cloud-based software as a service subscription costing $5,000 per month.
Expected to reduce the number of current incidents per annum by 50%.
The company currently has ten security incidents per annum at an average cost of $10,000 per incident. Which of the following is the ROI for this proposal after three years?
CAS-003 문제 48
Ann, a systems engineer, is working to identify an unknown node on the corporate network. To begin her investigative work, she runs the following nmap command string:
user@hostname:~$ sudo nmap -O 192.168.1.54
Based on the output, nmap is unable to identify the OS running on the node, but the following ports are open on the device:
TCP/22
TCP/111
TCP/512-514
TCP/2049
TCP/32778
Based on this information, which of the following operating systems is MOST likely running on the unknown node?
user@hostname:~$ sudo nmap -O 192.168.1.54
Based on the output, nmap is unable to identify the OS running on the node, but the following ports are open on the device:
TCP/22
TCP/111
TCP/512-514
TCP/2049
TCP/32778
Based on this information, which of the following operating systems is MOST likely running on the unknown node?
CAS-003 문제 49
Given the following:
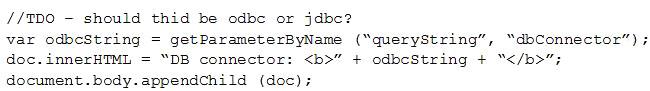
Which of the following vulnerabilities is present in the above code snippet?
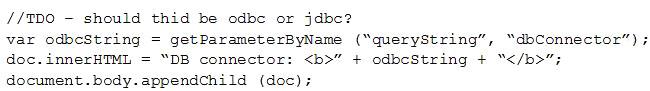
Which of the following vulnerabilities is present in the above code snippet?
CAS-003 문제 50
A threat advisory alert was just emailed to the IT security staff. The alert references specific types of host operating systems that can allow an unauthorized person to access files on a system remotely. A fix was recently published, but it requires a recent endpoint protection engine to be installed prior to running the fix.
Which of the following MOST likely need to be configured to ensure the system are mitigated accordingly? (Select two.)
Which of the following MOST likely need to be configured to ensure the system are mitigated accordingly? (Select two.)

